Search This Blog
We provide data, new trends, actors, intelligence, market dynamics (drivers, opportunities, restraints, challenges, etc.), analytics, advisory, technologies (apps, software, systems, algorithm, etc.), services, market data (consumers, revenue, investments, capital, etc.), actionable insights, information, consulting, etc.
Posts
Showing posts from March 3, 2015
Cloud numbers in telecoms industry: the onoff App paves its way.
- Get link
- X
- Other Apps
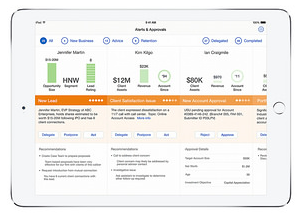
Learn how to evaluate a BI solution that is both flexible and secure for your organization.
- Get link
- X
- Other Apps
Mobile internet in Africa and Middle Eastern: The 3G Firefox OS smartphones pave their way.
- Get link
- X
- Other Apps