Search This Blog
We provide data, new trends, actors, intelligence, market dynamics (drivers, opportunities, restraints, challenges, etc.), analytics, advisory, technologies (apps, software, systems, algorithm, etc.), services, market data (consumers, revenue, investments, capital, etc.), actionable insights, information, consulting, etc.
Posts
Showing posts from July 28, 2015
Google Cloud Platform: Control over encryption in the public cloud.
- Get link
- X
- Other Apps
Critical vulnerabilities affecting Chrysler, Dodge, Jeep, and Ram models.
- Get link
- X
- Other Apps
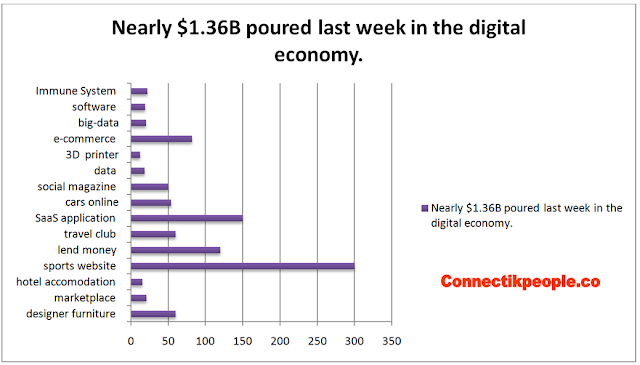
Nearly $1.36B poured last week in the digital economy.
- Get link
- X
- Other Apps