Search This Blog
We provide data, new trends, actors, intelligence, market dynamics (drivers, opportunities, restraints, challenges, etc.), analytics, advisory, technologies (apps, software, systems, algorithm, etc.), services, market data (consumers, revenue, investments, capital, etc.), actionable insights, information, consulting, etc.
Posts
Showing posts from April 20, 2015
Automate Security Compliance in Private and Public Clouds.
- Get link
- X
- Other Apps
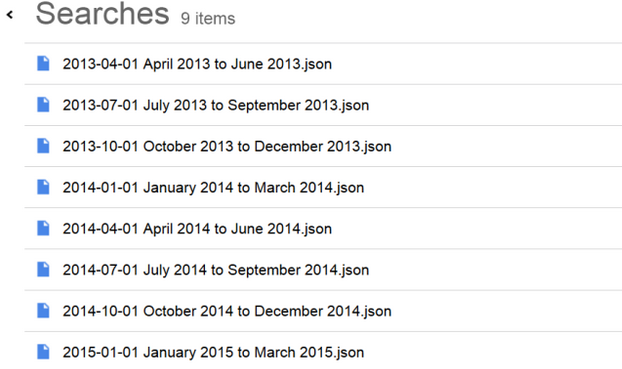
Download your past searches and delete your searches and browsing activity: stakes, process,realities and recommendations.
- Get link
- X
- Other Apps
Allow organizations to easily collaborate on security incidents.
- Get link
- X
- Other Apps