Search This Blog
We provide data, new trends, actors, intelligence, market dynamics (drivers, opportunities, restraints, challenges, etc.), analytics, advisory, technologies (apps, software, systems, algorithm, etc.), services, market data (consumers, revenue, investments, capital, etc.), actionable insights, information, consulting, etc.
Posts
Showing posts from March 23, 2015
We Increase sensitization and awareness around malicious Code
- Get link
- X
- Other Apps
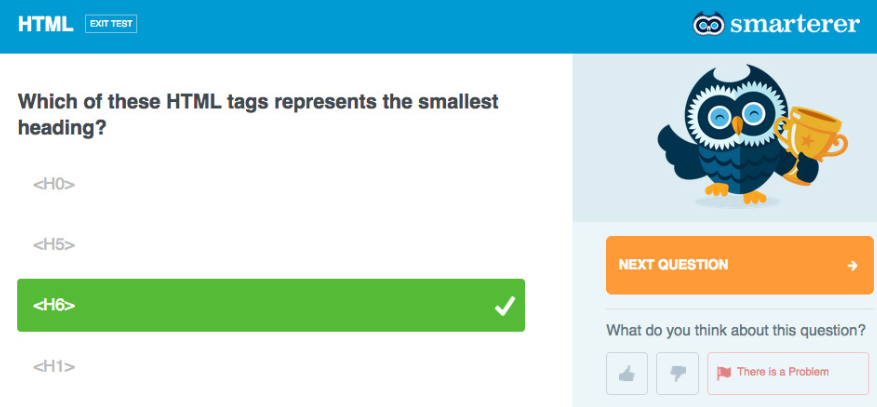
Close the gap between the skills you have and the skills you need in our digital-age.
- Get link
- X
- Other Apps
Next-generation systems of data encryption that leverage advanced cryptography technologies.
- Get link
- X
- Other Apps